6 Tips for Remote Employees
Thanks to increased use of technology in work, it has enabled a lot of persons to work less and less from the office. What this means is that we now have more persons working from the comfort of their homes, a coffee shop, hotel or some other remote location of their choosing.

Despite the many advantages of having employees work remotely, these advantages come at a cost, usually, in the form of data security. Normally, having your employees work in a traditional office space means you can monitor what comes in and goes out of your company’s network – the IT team can catch viruses early, password changes can be forced upon employees using auto-reminders, and regular security checks means you catch issues early and deal with them.
This ability to work from anywhere gives employees the needed flexibility, and for the employers, it means they can enjoy the services of talents from around the world without having to worry about the overhead occasioned from staffing.
However, with remote employees, you lose all of this control, and it leaves your network open to virus attacks, cyber leaks and all other forms of cyber threats. When things like this happen, financial, legal and reputational problems may result. Therefore, you need to have a system in place to protect your network when you have employees working remotely. You employees should follow the things below to protect your network.
• PROTECT THEIR DEVICES AT ALL TIMES
Often, most data-stealing malware that affects devices arrive via the web or email and to reduce the chances of a security breach you have to restrict access to personal web browsing and email. However, enforcing this is costly and can be difficult. Therefore, to protect your network, you have to ensure your employees use the latest versions of all applications and install security patches as soon as they are released. You can also manage things from your end by activating automatic updates from software makers.
• LIMIT THE USE OF PUBLIC WI-FI
Internet on public Wi-Fi is provided from unknown servers, and this means security is not guaranteed. This makes the network susceptible to hackers since anyone can access it; therefore, you should have a standing order which forbids your employees from sending or receiving sensitive information over public Wi-Fi. As with public Wi-Fi, so too is cyber café, your employees should not conduct company business with them.
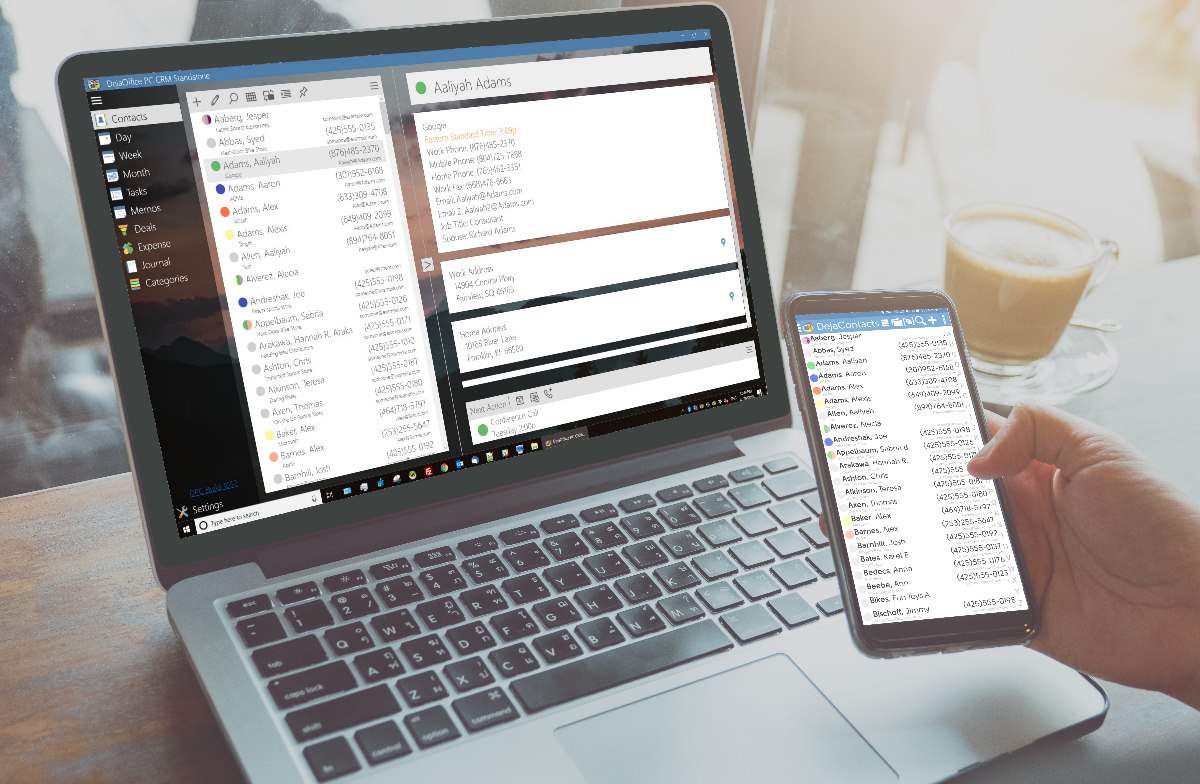
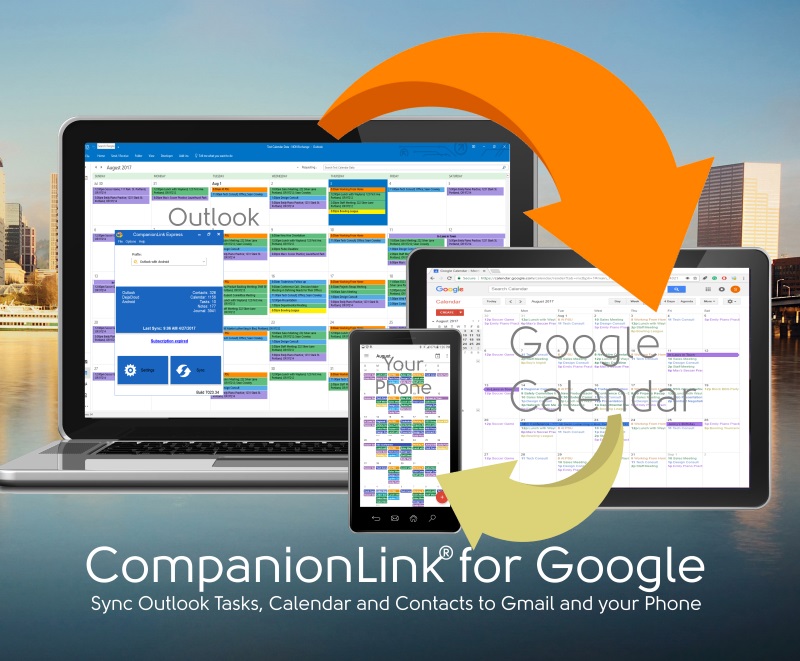
• EMPLOY CLOUD SERVICES
By employing cloud-based applications in your office tasks, it allows your employees to work from any location and transfers the burden of managing data security to the cloud service providers who usually are more equipped to handle it.
The cloud-based service provider gives you safe virtual storage and working space while your employees manage passwords. You should ensure your employees use strong passwords as this helps keep data secure. In fact, you can employ cloud applications to secure employees access to the web, and there are quite a number of companies which offer these services.
• LIMIT THE USE OF EXTERNAL STORAGE DEVICES
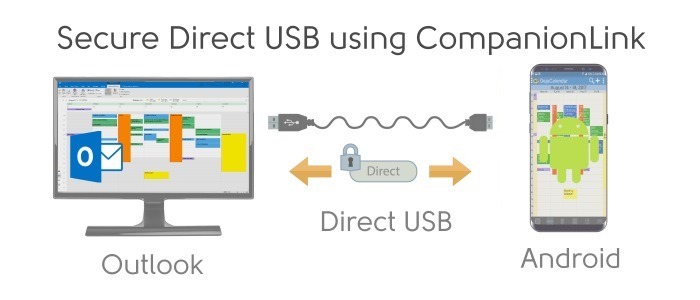
External storage devices like USBs can easily be misplaced so your remote employees should restrict their use and if they must be used to house only non-sensitive information.
Beyond this, USB devices can be used by hackers to install malware on your computer so your remote employees should avoid using a friend or stranger’s USB on their laptop.
• GET EDUCATION ON SECURITY TRAINING
Some companies may be tempted to give employees the benefit of the doubt by assuming they know how to manage security. However, this should not be the case as employees should be mandated to take up basic security courses which would teach them how to handle suspicious emails and links and to understand what a secure password should be like. It is important employees understand that work computers are for the company and not for personal use, therefore, should be treated as such.
• INSTALL ENCRYPTION SOFTWARE
Lost and stolen devices can pose a source of danger in the wrong hands, but you can lessen this risk with encryption software which bars unauthorized users from accessing the device.
Also, you can install remote wipes on your devices so data on them can be erased in case they go missing.
In conclusion, although remote workers can save the company money in terms of expenditure on overhead, they can also pose a risk to the firm especially if they use office devices for personal use. Therefore as a company, you have to put measures in place to handle staff remotely while remote workers should do their bit in adhering with safety measures.